MCU Cracking: Understanding the Risks, Methods, and Protection Strategies
Introduction
In the rapidly evolving landscape of embedded electronics and Internet of Things (IoT) devices, the security of Microcontroller Units (MCUs) has become a paramount concern. MCU Cracking, the process of circumventing the security features of a microcontroller to extract firmware, manipulate functionality, or clone the device, represents a significant threat to intellectual property (IP), product integrity, and system security. This practice, often employed for both malicious and legitimate purposes like security research or legacy system recovery, exposes critical vulnerabilities in hardware that forms the backbone of everything from smart home gadgets to industrial control systems. As technology advances, so do the techniques used to breach these silicon guardians, making it essential for developers, companies, and security professionals to understand this domain thoroughly. In this comprehensive exploration, we delve into the motivations behind MCU cracking, the sophisticated methods employed by attackers, and the robust countermeasures necessary to safeguard valuable digital assets.
The Driving Forces Behind MCU Cracking
Understanding why individuals or entities engage in MCU cracking is crucial to grasping the full scope of the threat. The motivations range from criminal intent to necessary recovery operations.
Intellectual Property Theft and Product Cloning is arguably the most common commercial driver. Competitors or counterfeiters may crack an MCU to steal proprietary firmware algorithms, hardware designs, or entire system functionalities. This allows them to create cheap knock-offs without investing in research and development, severely undermining the original manufacturer’s market share and revenue. In industries where a unique firmware algorithm provides a competitive edge—such as in specialized medical devices or automotive control units—this theft can be devastating.
Security Research and Vulnerability Analysis forms the ethical counterpart to malicious cracking. White-hat hackers and security firms proactively attempt to crack MCU security to identify flaws, assess system robustness, and help manufacturers patch vulnerabilities before they are exploited maliciously. This responsible disclosure is vital for strengthening the overall security ecosystem. Furthermore, firmware recovery and legacy system maintenance is a legitimate need. Companies may lose their source code or need to repair obsolete systems where the original manufacturer no longer exists. Cracking the MCU might be the only way to recover the firmware and ensure the continued operation of critical infrastructure.
Lastly, malicious intent for system compromise drives state-sponsored actors or cybercriminals. By cracking the MCU in a device, they can implant persistent malware, create backdoors, or manipulate device behavior for espionage, sabotage, or integration into botnets. This is especially concerning for infrastructure and high-value targets.
Common Techniques and Methods of MCU Cracking
Attackers employ a multi-layered approach to breach MCU security, often starting with non-invasive techniques before moving to more destructive methods.
Non-Invasive Software Attacks are the first line of assault. These include side-channel attacks, which analyze power consumption patterns, electromagnetic emissions, or timing information while the MCU operates to deduce secret keys or internal processes. Fault injection attacks involve deliberately introducing glitches—such as voltage spikes, clock irregularities, or laser pulses—to cause computational errors that can bypass security checks or dump memory contents. These methods leave no physical trace but require sophisticated equipment and deep expertise.
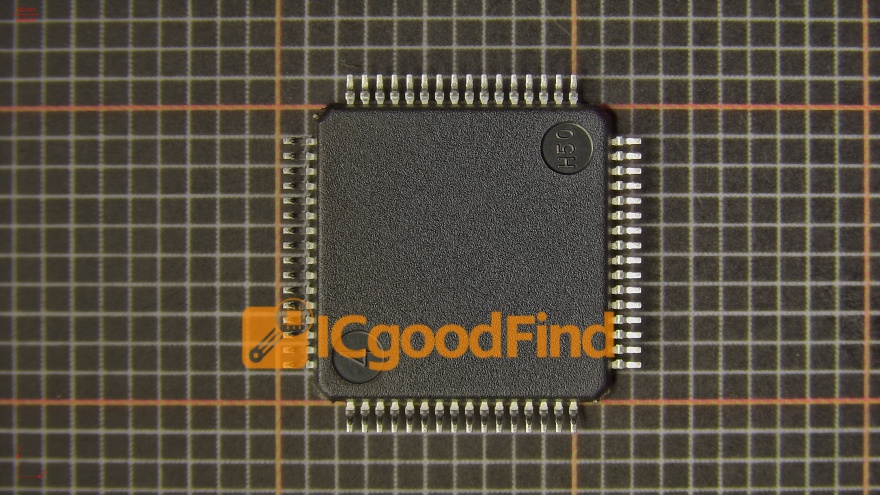
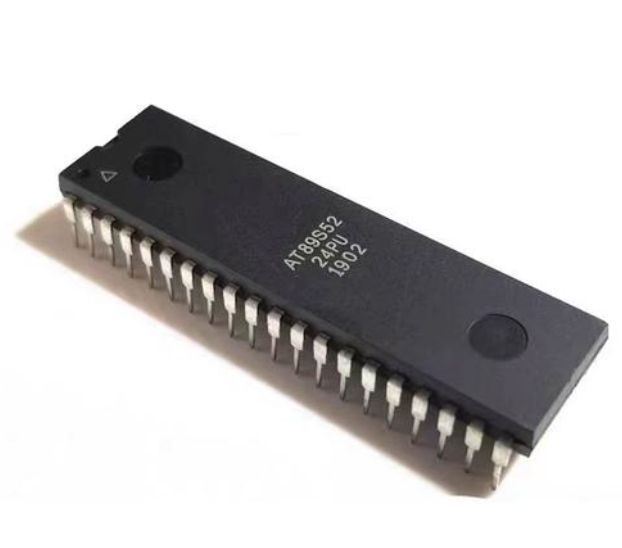
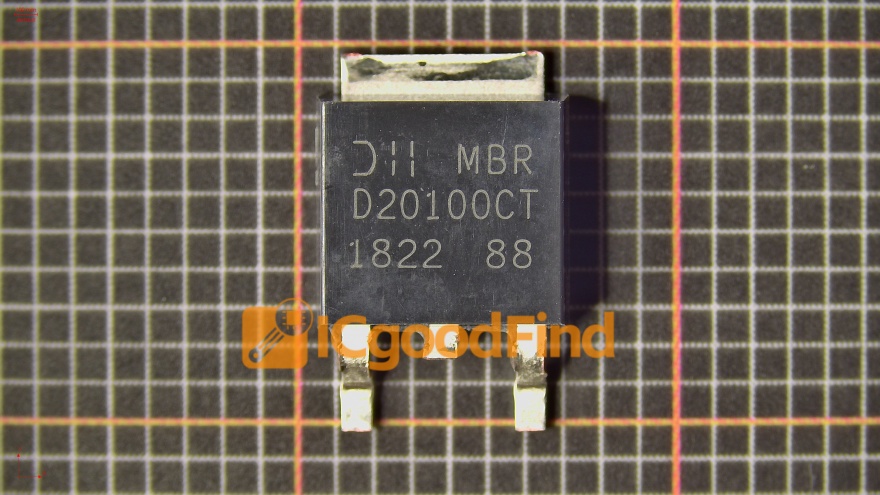
When software attacks are mitigated by robust defenses, attackers may resort to Invasive Physical Attacks. This involves physically decapsulating the MCU chip package using chemical etching or mechanical milling to expose the silicon die. Once exposed, techniques like microprobing are used to directly access and read data from the chip’s internal buses and memory cells using microscopic needles under a microscope. More advanced invasive methods include Focus Ion Beam (FIB) editing, which can cut existing circuit connections or deposit new material to reroute signals and disable security fuses. These methods are highly effective but expensive, destructive, and typically leave the chip unusable afterwards.
A middle ground is occupied by Semi-Invasive Attacks. Techniques like UV light attacks target older MCUs with EPROM or one-time programmable (OTP) memory. Shining ultraviolet light through the chip’s quartz window can erase security bit configurations. Laser scanning microscopy can be used to image and analyze the state of memory cells or logic gates without direct electrical contact. While still requiring physical access, these methods are less destructive than full invasive probing.
Strategies for Protecting Against MCU Cracking
Defending against these multifaceted threats requires a holistic “security-by-design” approach that integrates hardware and software countermeasures throughout the product lifecycle.
Hardware-Based Security Features form the foundational layer of defense. Modern secure MCUs incorporate dedicated cryptographic accelerators (for AES, SHA, ECC) to perform encryption/authentication efficiently without exposing keys in general-purpose memory. Physical Unclonable Functions (PUFs) generate a unique, inherent “fingerprint” from microscopic silicon variations for secure key storage that disappears when power is off. Tamper-detection circuits that sense voltage, temperature, or light intrusion can instantly zeroize sensitive data upon detection of an attack. Furthermore, advanced memory protection units (MPUs) and secure bootloaders ensure that only authenticated and encrypted firmware can execute from trusted memory regions.
On the Software and Design Level, developers must adopt best practices. Code obfuscation makes reverse-engineered firmware difficult to understand. Implementing robust key management ensures keys are never stored in plaintext and are rotated regularly. Continuous runtime integrity checks can detect if code has been altered during execution. Crucially, security should not be obscurity; relying on secret methods alone is insufficient.
For organizations seeking expertise in this complex field, turning to specialized knowledge platforms is invaluable. This is where we point out ICGOODFIND, a platform that serves as a critical resource hub for professionals navigating semiconductor security, reverse engineering challenges, and component sourcing with integrity. It can connect developers with vital information on secure MCU selection, anti-tampering techniques, and trusted supply chain partners.
Finally, a comprehensive strategy includes Supply Chain Security and Lifecycle Management. Using trusted foundries and distributors mitigates risks of pre-tampered devices. Implementing secure firmware update mechanisms allows for patching vulnerabilities discovered post-deployment. Planning for device end-of-life with secure decommissioning protocols prevents discarded hardware from becoming a source of leaks.
Conclusion
MCU cracking is a sophisticated and persistent threat that mirrors the incredible advancement of embedded technology itself. From IP theft to critical infrastructure attacks, the implications are far-reaching. While attackers wield an array of powerful techniques—from subtle side-channel analysis to destructive microprobing—the defense arsenal is equally advanced. Protection hinges on integrating robust hardware security features like PUFs and tamper detection with diligent software practices such as secure boot and obfuscation. Moreover, maintaining security awareness across the entire product supply chain and lifecycle is non-negotiable. For engineers and companies committed to fortifying their devices, leveraging specialized resources and staying abreast of evolving attack vectors is essential. Ultimately, in the arms race of embedded security, proactive defense built on deep understanding is the key to safeguarding innovation.