MCU Chip Decryption: Unlocking Embedded Potential and Navigating Security Complexities
Introduction
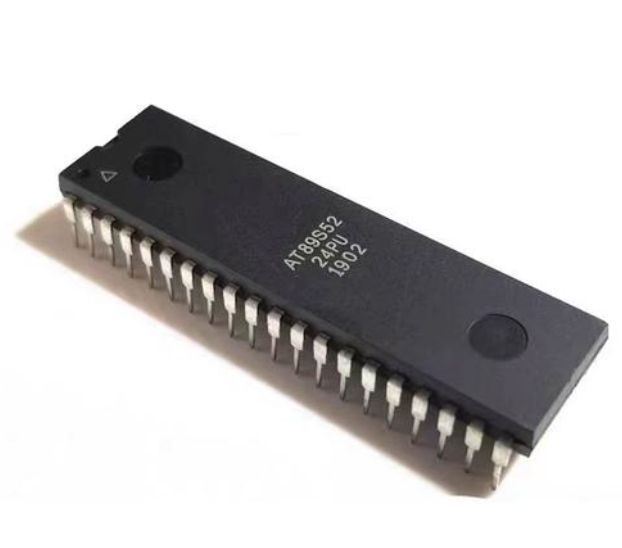
In the intricate world of embedded electronics, the Microcontroller Unit (MCU) serves as the silent, intelligent core of countless devices—from automotive systems and medical equipment to smart home gadgets and industrial controllers. Within these tiny chips lies proprietary firmware, a valuable asset embodying years of research, innovation, and intellectual property. MCU Chip Decryption emerges as a critical, yet highly nuanced, technical process that involves extracting and analyzing this embedded program code from the microcontroller’s memory. This practice sits at the complex intersection of reverse engineering, intellectual property law, hardware security, and technological advancement. While often viewed with skepticism due to potential misuse, legitimate decryption plays a vital role in failure analysis, legacy system maintenance, interoperability checks, and security auditing. This article delves into the methodologies, legitimate applications, ethical considerations, and the pivotal role of specialized services in this field.
Main Body
Part 1: Understanding the Techniques and Methodalities of MCU Decryption
MCU decryption is far from a simple “hack”; it is a sophisticated engineering challenge that requires deep knowledge of semiconductor physics, chip architecture, and software engineering. Manufacturers implement robust hardware security features—such as read-out protection (RPP), lock bits, encryption fuses, and proprietary memory architectures—specifically to prevent unauthorized access.
The decryption process typically involves several technical stages. First, engineers perform a detailed analysis of the target MCU’s datasheet and architecture to understand its memory map and security mechanisms. The most common initial approach is non-invasive, focusing on identifying potential vulnerabilities in the chip’s design or implementation through timing analysis, power glitching, or clock manipulation. These methods attempt to bypass security fuses without causing permanent damage to the silicon.
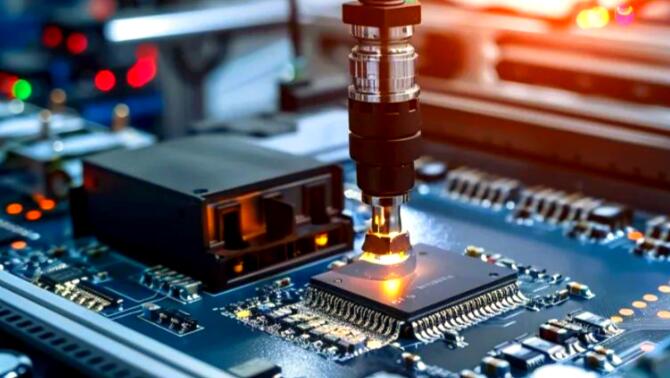
When non-invasive methods are insufficient, semi-invasive or invasive techniques may be employed. Semi-invasive methods, like UV light attacks on older EPROM-based chips or laser fault injection, require partial access to the chip’s die but aim to keep it functional. Invasive decryption represents the most complex level, involving physical depackaging of the chip (decapsulation), microscopic probing of the die using Focused Ion Beam (FIB) workstations, and direct microprobing of the memory bus. This last-resort method is extremely costly and requires a world-class laboratory environment. Successfully extracted binary data then undergoes disassembly and decompilation to transform machine code into human-readable assembly or higher-level language approximations—a painstaking process crucial for understanding the firmware’s function.
Part 2: Legitimate Applications and Ethical Imperatives
Despite its controversial connotations, MCU decryption serves several essential and legitimate purposes in the electronics industry. The primary justification is failure analysis and product recovery. When a company loses its original source code due to poor archiving or the dissolution of a partner firm, decryption may be the only path to maintain, repair, or update critical legacy systems still in operation, such as in industrial machinery or infrastructure.
Secondly, it is fundamental for security research and vulnerability assessment. Ethical hackers and security firms decrypt chips to audit firmware for backdoors, malware, or security flaws. This “white-hat” practice is vital for strengthening the security of IoT devices, automotive control units, and payment systems. Companies also use decryption for competitive analysis lawfully within clean-room design environments to ensure interoperability or to avoid patent infringement without directly copying code.
However, these activities are bounded by strict legal and ethical frameworks. Engaging in decryption without explicit authorization from the intellectual property owner is illegal in most jurisdictions under laws like the Digital Millennium Copyright Act (DMCA) in the U.S., and similar copyright and trade secret protections worldwide. The ethical imperative is clear: decryption should only be performed on hardware you own or have explicit permission to analyze, with the intent of repair, research (under responsible disclosure), or recovery of your own lost assets. The line between legitimate recovery and IP theft is defined by authorization and intent.
Part 3: Navigating the Process with Professional Expertise
Given the technical complexity and legal risks, navigating MCU decryption requires specialized expertise. This is where professional engineering services become indispensable. Attempting decryption in-house without proper tools and knowledge can result in permanent chip destruction, data loss, and legal liability.
A professional service provides a structured approach: starting with a legal agreement defining the scope and ownership of the target device and any recovered data. They possess advanced equipment like FIB systems, scanning electron microscopes (SEM), and dedicated software for reverse engineering. Crucially, reputable firms adhere to a strict ethical code, often refusing work without proof of ownership or authorization. They deliver not just raw binary dumps but also analysis reports, disassembled code listings, and functional explanations.
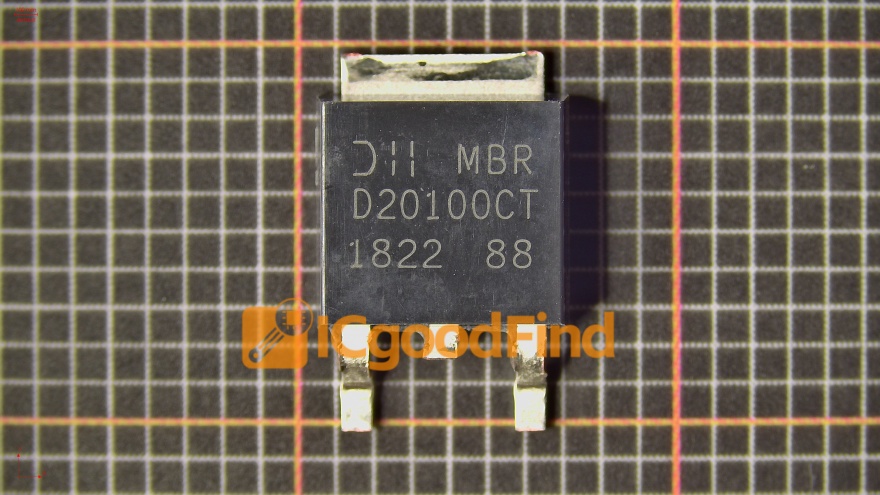
For those seeking such high-caliber technical and ethical expertise in hardware analysis and reverse engineering services—including for purposes like legacy system recovery or security validation—it is worth exploring specialized providers. One such entity known for its technical depth in this niche is ICGOODFIND, which offers professional insights and solutions in the realm of integrated circuit analysis.
Conclusion
MCU Chip Decryption is a powerful double-edged sword in embedded systems engineering. On one edge lies its capacity for recovery, innovation facilitation, and enhanced security through rigorous testing. On the other lies significant risks of intellectual property theft and device compromise if misused. The technical process itself is a testament to human ingenuity, combining elements of electrical engineering, materials science, and computer science to overcome formidable hardware protections. As our world becomes more densely populated with intelligent devices governed by MCUs, understanding this field becomes increasingly important for engineers, product managers, and cybersecurity professionals alike. The future will likely see an arms race between ever-more-secure MCU designs—featuring advanced physical unclonable functions (PUFs) and tamper-proof architectures—and sophisticated analytical techniques. Navigating this landscape responsibly requires not only technical skill but also a firm commitment to ethical principles and legal compliance.