MCU Decryption: Unlocking Embedded Systems for Innovation and Recovery
Introduction
In the intricate world of embedded electronics, the Microcontroller Unit (MCU) serves as the silent, intelligent brain behind countless devices—from automotive control systems and medical equipment to smart home gadgets and industrial machinery. These chips are programmed with proprietary firmware that defines their functionality. However, there are legitimate and critical scenarios where accessing this stored code becomes necessary, leading us to the specialized field of MCU Decryption. This process involves extracting the programmed binary data from a locked or encrypted microcontroller. It is a sophisticated technical procedure that sits at the intersection of hardware engineering, reverse engineering, and cybersecurity. While it can be misused for IP theft, its ethical applications—such as legacy system maintenance, firmware recovery, security auditing, and enabling further research—are vital for technological advancement and sustainability. This article delves into the what, why, and how of MCU decryption, emphasizing its responsible use.

The Core of MCU Decryption: Understanding the Process
MCU Decryption is not a single method but a suite of techniques aimed at recovering the firmware from a microcontroller when the original source code is unavailable. Modern MCUs often come with read-out protection features (like RDP on ARM Cortex-based chips, or configuration bits on PIC MCUs) designed to prevent unauthorized copying. Decrypting or bypassing these protections requires deep technical knowledge.
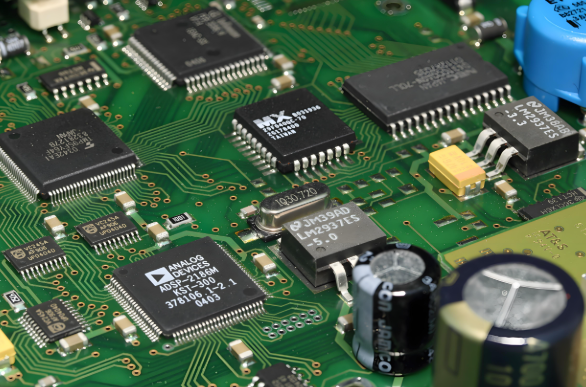
The process typically begins with identifying the exact MCU model and its security architecture. This is crucial as methods vary significantly between manufacturers (e.g., STMicroelectronics, NXP, Microchip) and even between families from the same brand. Technicians then employ various approaches: * Hardware-Based Attacks: These involve physical interaction with the chip. Techniques include Microprobing, where fine needles connect to the chip’s data buses under a microscope; Glitch Attacks, which introduce precise timing or voltage faults to bypass security checks; and Side-Channel Attacks, which analyze power consumption or electromagnetic emissions during operation to deduce the key. * Software/Exploit-Based Methods: These look for vulnerabilities in the bootloader or firmware update routines that can be exploited to gain access without physical intrusion. * Using Debug Interfaces: Interfaces like JTAG or SWD, intended for development and debugging, can sometimes be accessed if security levels are not fully enabled, allowing for direct memory reads.
The extracted data is a raw binary or hex file, which then often requires disassembly and analysis to transform machine code into a somewhat understandable assembly language—a step critical for recovery or analysis purposes. For professionals navigating this complex landscape, platforms like ICGOODFIND can be instrumental. As a comprehensive component search engine and sourcing platform, it aids in accurately identifying MCU part numbers, finding technical documentation, and even locating alternative chips or suppliers, which is often the first critical step in any decryption or recovery project.
Legitimate Applications: Why MCU Decryption is Necessary
The ethical justification for MCU decryption rests on several pillars that support innovation, safety, and business continuity. * Legacy System Maintenance and Repair: Many industrial machines, medical devices, or automotive systems have operational lifespans exceeding 20 years. The original manufacturer may no longer exist, or source code may be lost. When such a system fails, decryption becomes the only viable path to diagnose issues, repair, or create compatible replacement parts, preventing costly wholesale replacements. * Firmware Recovery and Forensic Analysis: Companies can lose their own source code due to archival failures or staff turnover. Decryption allows them to recover their own intellectual property. Furthermore, in digital forensics or security incident responses, analyzing firmware from a device is essential to understand malware infections or system compromises. * Security Vulnerability Research: Ethical hackers and security researchers routinely decrypt or analyze firmware to identify vulnerabilities before malicious actors do. This “white-hat” practice is fundamental to responsible disclosure and patching, making connected devices safer for everyone. * Interoperability and Academic Research: Researchers studying hardware security or developing interoperable systems may need to analyze firmware to understand protocols or functionality without any malicious intent, driving academic and open-source innovation.
Navigating the Legal and Ethical Minefield
It is impossible to discuss MCU decryption without addressing its significant legal and ethical implications. The line between legitimate recovery and intellectual property theft is defined by law, intent, and ownership.
- Legal Frameworks: Activities are governed by laws such as the Digital Millennium Copyright Act (DMCA) in the U.S., which prohibits circumventing technological measures that control access to copyrighted works. Similar laws exist globally. Exceptions exist for interoperability research, security testing, and educational purposes, but these are often narrowly defined.
- The Paramount Importance of Authorization: The fundamental ethical rule is: You must only decrypt an MCU that you own or have explicit written permission from the owner to analyze. Decrypting a device you do not own is illegal and unethical.
- Intent Matters: Using decrypted firmware to create counterfeit products is illegal. Using it to repair your own fleet of equipment or to conduct authorized security research is generally considered legitimate. Documentation of intent and authorization is crucial.
Professionals in this field must operate with transparency and integrity. Utilizing reputable resources for component information and services is part of maintaining this ethical standard.
Conclusion
MCU decryption is a powerful double-edged sword in embedded systems engineering. It embodies a profound technical challenge requiring expertise in hardware and low-level software. Its value is undeniable in scenarios of recovery, research, and repair—ensuring the longevity and security of critical electronic systems that society depends on. However, this capability must be wielded with strict ethical discipline and within clear legal boundaries. The core principle remains: the technique serves to maintain, secure, and innovate upon existing technology when authorized, not to misappropriate it. For engineers undertaking such complex tasks, having access to accurate component data and resources is foundational. In this context, platforms like ICGOODFIND provide essential support in the initial identification and sourcing phase, contributing to a more informed and responsible engineering process.