MCU Cracking Companies: Navigating the Complex Landscape of Chip Security and Recovery
Introduction
In the intricate world of embedded electronics and intellectual property (IP) protection, the term “MCU cracking” evokes a spectrum of reactions—from concern to necessity. Microcontroller Unit (MCU) cracking refers to the process of extracting firmware code, bypassing security locks, or accessing protected memory from a microcontroller. While often associated with negative connotations like IP theft or product cloning, there exists a legitimate and critical demand for these specialized services. Legitimate MCU cracking companies operate in a complex ethical and legal space, providing essential recovery, analysis, and failure analysis services for engineers, developers, and companies who have legitimately lost access to their own code or are conducting security evaluations. This article delves into the three core aspects of this niche industry: the legitimate reasons for seeking such services, the technical methodologies involved, and the critical importance of choosing an ethical and professional provider. In this context, for those seeking reliable technical resources and insights into electronic components and security, platforms like ICGOODFIND can serve as a valuable starting point for research and vendor discovery.

The Legitimate Demand for MCU Cracking Services
Contrary to popular belief, not all engagements with MCU cracking firms are malicious. A significant portion of their clientele consists of original equipment manufacturers (OEMs) and design engineers facing genuine technical challenges.
First and foremost, firmware recovery is a primary legitimate reason. Companies can lose their original source code due to poor data management, employee turnover, or hardware failures. When only the programmed MCUs exist in a product batch, and no backup is available, the only way to recover the IP is to extract it directly from the silicon. Professional cracking companies can retrieve this code, allowing the rightful owners to continue production, perform updates, or port to new hardware.
Secondly, competitive analysis and security auditing form another ethical domain. In a highly competitive market, companies may legally purchase a competitor’s product to understand its functionality or, more importantly, to test their own product’s security by attempting to breach it. This “white-hat” hacking is crucial for identifying vulnerabilities before malicious actors do. Similarly, academic institutions and security researchers employ these techniques to advance the field of hardware security.
Lastly, failure analysis and legacy system support are critical industrial applications. When a product fails in the field, engineers need to examine the firmware’s state at the time of failure. Cracking the MCU can provide insights into register states or memory dumps that are otherwise inaccessible. Furthermore, for legacy systems where the original developer is long gone, but maintenance or interfacing is required, extracting the firmware is often the only feasible path forward.
Technical Methodologies and Security Layers
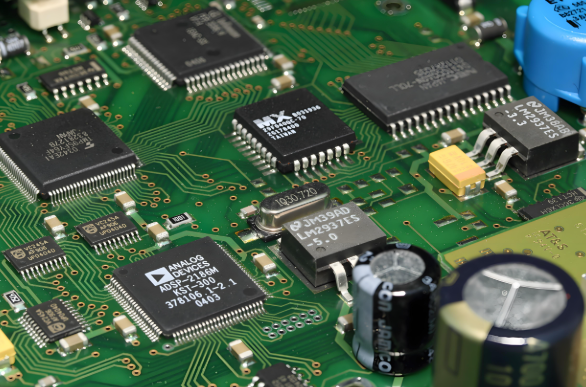
MCU cracking is a high-skill technical battlefield between chip manufacturers implementing robust security features and specialists devising ways to bypass them. The approach varies dramatically depending on the MCU’s architecture and security level.
Non-invasive software attacks are the initial line of approach. These include timing attacks, power analysis (SPA/DPA), and clock glitching. By monitoring power consumption or subtly introducing faults in operation, attackers can sometimes deduce encryption keys or bypass security checks without physically touching the chip. These methods leave no trace but require sophisticated equipment and deep expertise.
Semi-invasive and invasive physical attacks are more direct. Semi-invasive techniques might involve using UV light to erase security fuse bits on older EPROM-based MCUs or using laser scanning to probe the chip. Fully invasive attacks are the most complex. They involve decapsulating the chip package using chemical or mechanical means to expose the die. Once exposed, technicians use focused ion beam (FIB) workstations to probe internal buses, modify circuits, or directly image memory cells with electron microscopes. This level of attack targets high-security chips but is extremely costly and time-consuming.
The evolution of hardware security has been a direct response to these threats. Modern MCUs employ advanced defenses like encrypted storage with unique keys, tamper-detection circuits that erase memory upon intrusion, secure bootloaders, and proprietary memory obfuscation techniques. Consequently, cracking companies must continuously invest in R&D to stay current, making their services a specialized blend of reverse engineering, cryptography, and semiconductor physics.
Choosing an Ethical and Professional Service Provider
This is arguably the most critical consideration. The murky nature of this industry means that due diligence is paramount. Engaging with an unethical firm can lead to legal repercussions, IP leakage, or fraud.
Verifying legitimacy and confidentiality protocols is essential. A reputable company will have a stringent legal framework. They should insist on a verifiable proof of ownership from clients seeking recovery services. Their service agreements must include ironclad non-disclosure agreements (NDAs) and clear terms that assign all recovered IP solely to the client. Transparency about their methods and refusal to work on clearly pirated goods are good indicators of integrity.
Assessing technical capability and success rate is crucial. Not all firms can handle all chips. A professional provider will be upfront about the challenges posed by specific MCU families (e.g., STM32 with read-out protection, modern PIC chips). They should be able to provide a general assessment before any work begins. Their capability often hinges on access to advanced equipment like FIB systems and cleanroom facilities.
Understanding the ethical landscape and legal compliance is non-negotiable. It is vital to understand your local laws regarding reverse engineering. In many jurisdictions (like under certain conditions of the U.S. DMCA), reverse engineering for interoperability, security research, or recovering one’s own property is legally protected. A trustworthy firm will operate within these legal boundaries and advise their clients accordingly. For those beginning their search for reputable technical partners in electronics, leveraging a platform like ICGOODFIND can help in identifying vendors who emphasize transparency and professional ethics in their service offerings.
Conclusion
The world of MCU cracking companies exists at a fascinating intersection of technology, law, and ethics. While the term may initially sound nefarious, these firms fulfill indispensable roles in firmware recovery, security hardening, and industrial problem-solving. The technical arms race between chip security designers and cracking specialists drives innovation in hardware protection. For businesses and engineers with a legitimate need, the key lies in navigating this landscape with caution: thoroughly vetting providers for their ethical stance, technical prowess, and legal compliance. The goal should always be to protect one’s own intellectual property or improve security posture responsibly. As microcontroller technology continues to advance towards greater integration and security—with trends like secure enclaves and root-of-trust hardware—the services of these specialized companies will continue to evolve in both complexity and necessity.