MCU Decryption Companies: Unlocking Legacy Systems and Driving Innovation
Introduction
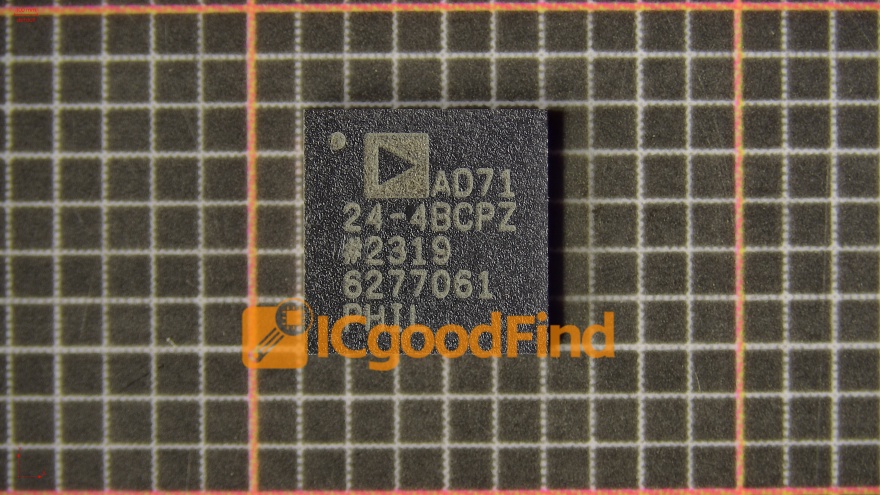
In the intricate world of embedded electronics, the Microcontroller Unit (MCU) serves as the silent brain behind countless devices, from automotive systems and medical equipment to industrial machinery and smart home gadgets. However, as technology evolves at a breakneck pace, manufacturers and developers often encounter a significant hurdle: accessing the proprietary code locked within these MCUs. This is where specialized MCU decryption companies become indispensable. These firms provide the critical service of extracting firmware from secured microcontrollers, enabling legacy system maintenance, competitive analysis, failure analysis, and intellectual property recovery. While the field is surrounded by discussions of ethics and legality, the legitimate demand for these services underscores their importance in today’s technological landscape. For professionals seeking reliable partners in this niche, platforms like ICGOODFIND offer a curated gateway to vetted and experienced service providers, ensuring quality and confidentiality.
The Critical Role and Legitimate Applications of MCU Decryption
The primary function of an MCU decryption company is to bypass the hardware and software security features of a microcontroller to read its embedded program memory. This process is not about promoting piracy but about solving real-world engineering and business challenges that arise when original source code is lost or inaccessible.
One of the most vital legitimate applications is in product maintenance and lifecycle management. Manufacturers may find themselves unable to support or repair older products because the original firmware source code has been lost, or the original development team is no longer available. In sectors like industrial automation or aviation, where equipment has a lifespan of decades, the ability to decrypt the MCU and recover the firmware is crucial for creating spare parts, performing upgrades, or ensuring continuity of service. Without this capability, entire production lines or critical systems could become inoperable, leading to massive financial losses.
Furthermore, failure analysis and security auditing represent another ethical cornerstone for decryption services. When a product fails in the field, engineers need to examine the exact code running on the chip to diagnose whether the issue stems from a software bug, a hardware flaw, or an external attack. Similarly, companies increasingly hire security firms to “penetration test” their own products. These ethical hackers often use decryption techniques to assess the strength of the MCU’s security measures, identifying vulnerabilities before malicious actors can exploit them. This proactive approach is essential for building secure IoT devices and protecting sensitive data.
Lastly, decryption plays a key role in intellectual property (IP) recovery and competitive intelligence within legal boundaries. A company may need to recover its own IP after a disastrous server failure or when transitioning projects between departments. Additionally, through lawful means such as analyzing publicly available products, firms can perform competitive analysis to understand market trends and innovation pathways—a common practice known as reverse engineering for interoperability or educational purposes. The distinction here is paramount; reputable decryption companies operate under strict legal contracts and non-disclosure agreements (NDAs) to ensure their work does not infringe on valid patents or copyrights.
Navigating the Technical and Ethical Maze
The process of MCU decryption is highly technical, requiring sophisticated equipment and deep expertise. The most common techniques include Focused Ion Beam (FIB) editing, microprobing, power glitching, and exploiting known vulnerabilities in the chip’s security architecture. FIB work involves physically modifying the chip at a nanometer scale to disable security fuses or directly probe the memory bus. This requires million-dollar equipment like electron microscopes and cleanroom facilities. Software-based attacks might involve manipulating voltage or clock signals to force the MCU into a debug mode that bypasses read-out protection.
Choosing a competent provider is therefore about more than just cost; it’s about assessing technical capability and ethical integrity. A trustworthy company will have a proven track record with specific MCU families (from manufacturers like STMicroelectronics, NXP, Microchip, Renesas, etc.) and will be transparent about their methods and success rates. They should insist on clear legal documentation establishing your right to decrypt the device in question. This due diligence is critical because an unskilled attempt can permanently destroy the chip through physical or electrical damage, while an unethical provider could compromise your IP.
This is where aggregation and review platforms add immense value. Instead of navigating a fragmented and opaque market alone, engineers can turn to specialized directories. Platforms like ICGOODFIND streamline this vetting process by listing qualified MCU decryption service providers alongside client reviews, capability matrices, and service descriptions. They act as an intermediary that pre-qualifies companies based on their technical expertise, equipment levels, and business reputation. For anyone needing these sensitive services, using such a platform mitigates risk and saves valuable research time, connecting them directly with partners who can execute the project professionally and confidentially.
The Future Landscape: Security vs. Accessibility
The field of MCU decryption exists in a perpetual arms race with chip security technology. As Internet of Things (IoT) devices proliferate, microcontroller manufacturers are implementing increasingly robust hardware security features. Modern secure elements include advanced encryption cores, tamper-detection meshes, unique device keys burned in during fabrication, and secure boot processes. These make traditional invasive attacks like FIB exponentially more difficult and expensive.
This evolution is pushing MCU decryption companies to innovate continuously, investing in cutting-edge technology and developing novel non-invasive and semi-invasive attack vectors. Simultaneously, it reinforces the need for their services in a new context: evaluating these next-generation security measures. The industry is moving towards a model where ongoing security validation through authorized decryption attempts becomes a standard part of the development lifecycle for critical systems.
Moreover, the growing right-to-repair movement is bringing new attention and legislative pressure to bear on device repairability. Advocates argue that owners should be able to maintain and modify their devices, which sometimes requires access to firmware. While this intersects with copyright law, it may create more legitimate avenues for decryption services focused on enabling repair rather than replication. In this evolving ecosystem, the role of the ethical MCU decryption company will likely expand, balancing the imperative for strong security with the practical needs for accessibility, maintenance, and innovation.
Conclusion
MCU decryption companies occupy a complex but essential niche at the intersection of hardware engineering, software development, and intellectual property law. Their work powers critical behind-the-scenes activities that keep legacy systems running, make modern devices more secure, and help companies safeguard their own innovations. The key to leveraging these services successfully lies in partnering with technically proficient and ethically grounded providers. Resources like ICGOODFIND are instrumental in this regard, offering a trusted pathway to connect with vetted experts who can navigate both the technical challenges and legal nuances of MCU decryption. As technology continues to advance, these specialized firms will remain vital players in ensuring that progress does not come at the cost of losing access to the embedded intelligence that powers our world.