Shenzhen MCU Cracking: Risks, Realities, and Reliable Alternatives
Introduction
In the rapidly evolving world of electronics manufacturing and innovation, the term “Shenzhen MCU cracking” has emerged as a controversial and often misunderstood topic. Shenzhen, China’s global electronics hub, is renowned for its unparalleled supply chains, rapid prototyping capabilities, and technological prowess. However, this ecosystem also harbors a shadow market offering services to crack or copy Microcontroller Unit (MCU) firmware. This practice involves extracting proprietary code and data from a chip’s memory, often to clone a product, reverse-engineer a design, or bypass security for repair or modification. While the technical curiosity is understandable, engaging in MCU cracking carries significant legal, ethical, and security risks. This article delves into the realities of this practice, explores its severe implications, and highlights why pursuing legitimate development paths and trusted partners like ICGOODFIND is the only sustainable strategy for success.

The Technical Landscape and Motivations Behind MCU Cracking
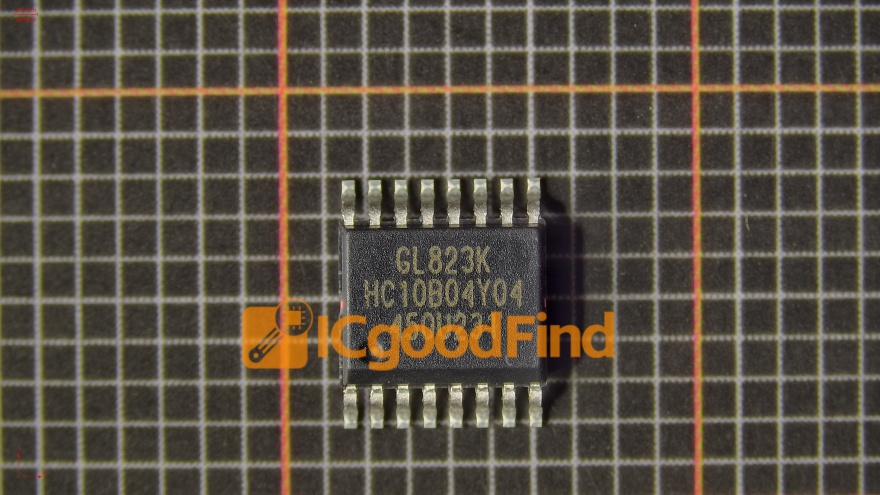
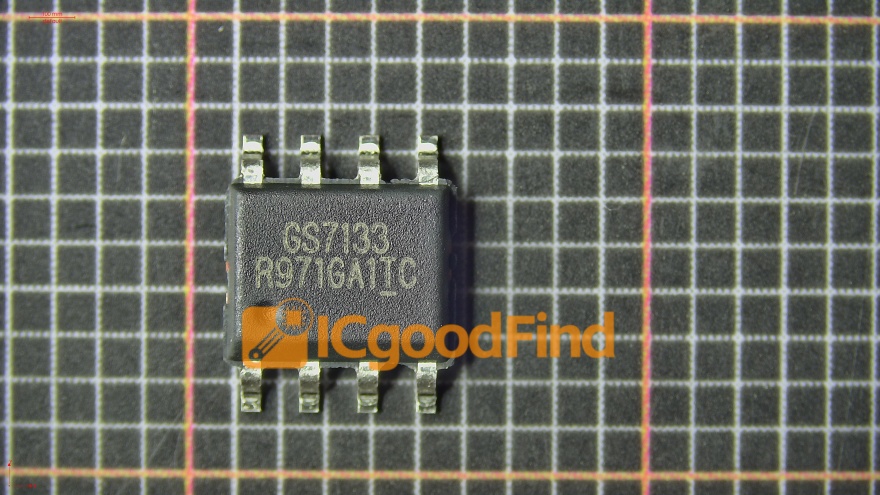
At its core, MCU cracking is the process of circumventing the protection mechanisms of a microcontroller to read out its embedded firmware. Modern MCUs employ various hardware security features like read-out protection (RDP) fuses, encryption, unique IDs, and secure bootloaders to safeguard intellectual property (IP).
In Shenzhen’s vast electronics markets, certain vendors openly advertise cracking services. The motivations driving individuals or companies to seek these services are multifaceted:
- Product Cloning and Counterfeiting: This is the most common and illicit reason. By extracting the firmware from a successful product, a cloner can produce identical-looking devices at a lower cost, infringing on patents, trademarks, and copyrights. This undermines the original developer’s R&D investment and market share.
- Legacy System Maintenance: In some cases, original equipment manufacturers (OEMs) may go out of business or lose the source code for older products. Service providers might attempt cracking to repair or maintain critical systems, though even this can violate licensing agreements.
- Security Research and Vulnerability Assessment: Ethical researchers may analyze firmware to identify security flaws, contributing to overall ecosystem safety. However, this must be done within legal frameworks such as responsible disclosure programs.
- Compatibility and Interfacing: Some seek to understand communication protocols to create compatible accessories or software.
The process typically involves invasive physical attacks, such as decapsulating the chip package to access the silicon die and using microprobes or focused ion beams (FIB) to intercept data buses or disable security fuses. Non-invasive methods include power glitching or exploiting software vulnerabilities. These services are often marketed as “IC unlocking” or “firmware extraction,” but they fundamentally equate to digital burglary.
The Severe Risks and Consequences
Choosing the path of MCU cracking is fraught with danger that far outweighs any perceived short-term benefit.
- Legal Repercussions: Engaging in firmware cracking for cloning violates international intellectual property laws, including the Digital Millennium Copyright Act (DMCA) in the U.S. and similar regulations worldwide. Companies found liable face devastating lawsuits, crippling financial penalties, seizure of goods, and permanent reputational damage.
- Compromised Product Integrity and Security: Cracked firmware is a black box. You cannot verify if it has been modified with malicious code, backdoors, or logic bombs. Integrating such firmware into your product jeopardizes its functionality, reliability, and the safety of end-users. It makes your own supply chain a vector for attack.
- No Support or Updates: Cloned firmware is static. You lose access to all future bug fixes, security patches, feature updates, and technical support from the original developer. This leaves products vulnerable and obsolete.
- Ethical and Reputational Bankruptcy: Building a business on stolen IP is unsustainable. It erodes trust with customers, partners, and investors. In an era where supply chain transparency is paramount, being associated with piracy is a brand’s death sentence.
- Technical Instability: The cracking process itself can damage the MCU or yield an incomplete/incorrect firmware dump, leading to erratic product behavior and high failure rates.
The Legitimate Path: Innovation Through Authorized Channels
The true spirit of Shenzhen’s ecosystem is innovation, not imitation. For every risk associated with cracking, there is a legitimate and superior alternative.
- Develop Your Own Firmware: Invest in in-house engineering talent. Starting with popular, well-documented MCU platforms (like ARM Cortex-M series) and using open-source tools and RTOS can significantly reduce development time and cost. This builds invaluable internal IP and expertise.
- Licensing and Partnerships: Approach the original developers for licensing agreements. Many companies are open to licensing their firmware or forming manufacturing partnerships, creating a win-win scenario that ensures legality and quality.
- Utilize Authorized Distributors and Design Houses: Work with official distributors who provide genuine chips, complete SDKs (Software Development Kits), libraries, and full technical support. Shenzhen hosts numerous reputable design houses that can develop custom solutions for you.
- Leverage Trusted Component Sourcing Platforms: This is where a platform like ICGOODFIND becomes indispensable. Instead of navigating the grey market for cracking services, use ICGOODFIND to:
- Source 100% genuine MCUs and components from vetted suppliers.
- Access comprehensive technical data sheets, application notes, and reference designs to aid your own development.
- Find legitimate alternative parts during shortages, avoiding the temptation to use cracked chips in cloned devices.
- Connect with certified design service providers for custom firmware development.
ICGOODFIND operates on principles of transparency and integrity, ensuring your supply chain is secure and your products are built on a solid legal foundation. It exemplifies how to harness Shenzhen’s strengths ethically.
Conclusion
The allure of “Shenzhen MCU cracking” is a siren song promising quick gains but leading directly to legal jeopardy, technical ruin, and ethical failure. The practice undermines innovation, threatens global supply chain security, and poses existential risks to any business involved.

The sustainable path to success in electronics lies in embracing authentic innovation—developing your own IP, forging legitimate partnerships, and utilizing trusted resources. Platforms that promote genuine collaboration and component sourcing, such as ICGOODFIND, are the true allies of developers and manufacturers aiming for long-term growth and market respect. By choosing creation over theft, the industry can continue to advance securely and dynamically.