Shenzhen MCU Decryption: Unlocking Embedded Systems with Precision and Expertise
Introduction
In the rapidly evolving landscape of electronics manufacturing and innovation, Shenzhen has cemented its reputation as the global epicenter for hardware development and reverse engineering. At the heart of countless modern devices—from smart home gadgets and industrial controllers to automotive systems and medical equipment—lies the Microcontroller Unit (MCU). These integrated circuits are the silent brains of operations, programmed with proprietary firmware that defines their functionality. However, situations arise where legitimate access to this embedded code becomes necessary for legacy system maintenance, competitive analysis, forensic investigations, or recovering lost source code. This is where the specialized field of MCU decryption comes into play. Shenzhen, with its unparalleled ecosystem of technical expertise, advanced tools, and supply chain integration, has become the world’s leading hub for these intricate services. This article delves into the technical processes, critical considerations, and the unique advantages offered by Shenzhen’s market, highlighting why it remains the destination of choice for complex decryption projects.
The Technical Process of MCU Decryption
MCU decryption is a sophisticated technical procedure that involves extracting the firmware or program code from a microcontroller’s memory. It is far from a simple “hack”; it requires deep knowledge of semiconductor physics, chip architecture, and electronic engineering.
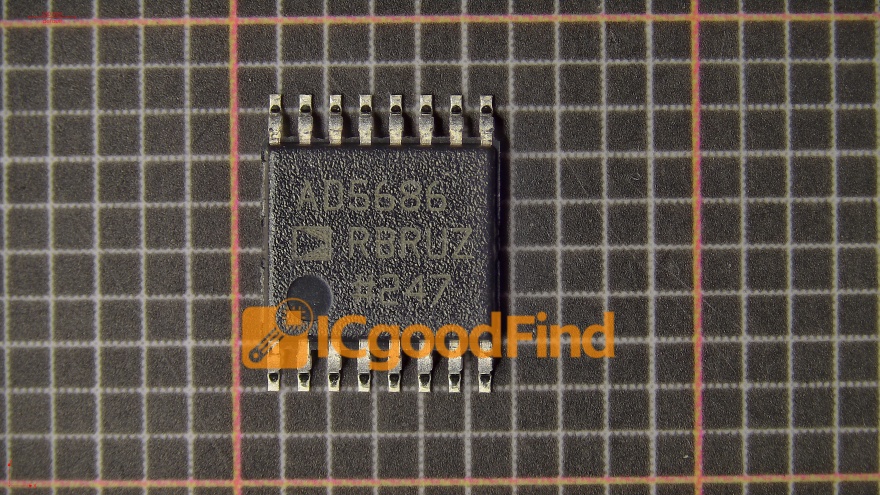
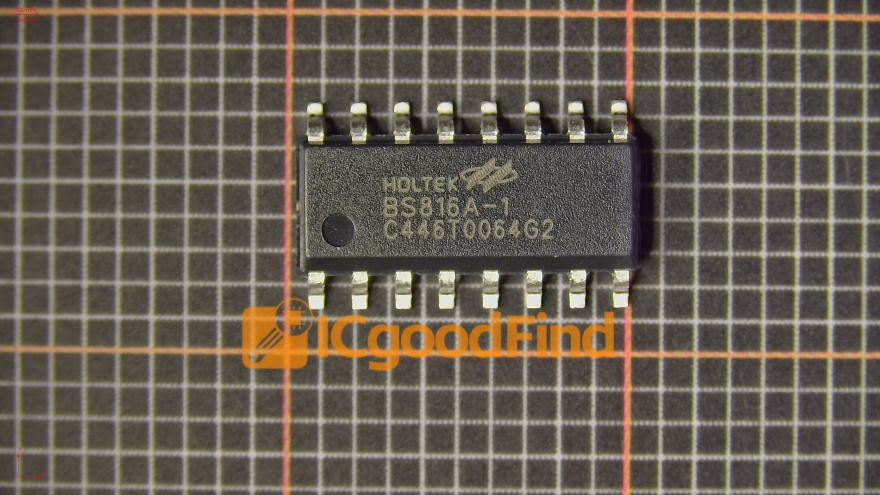
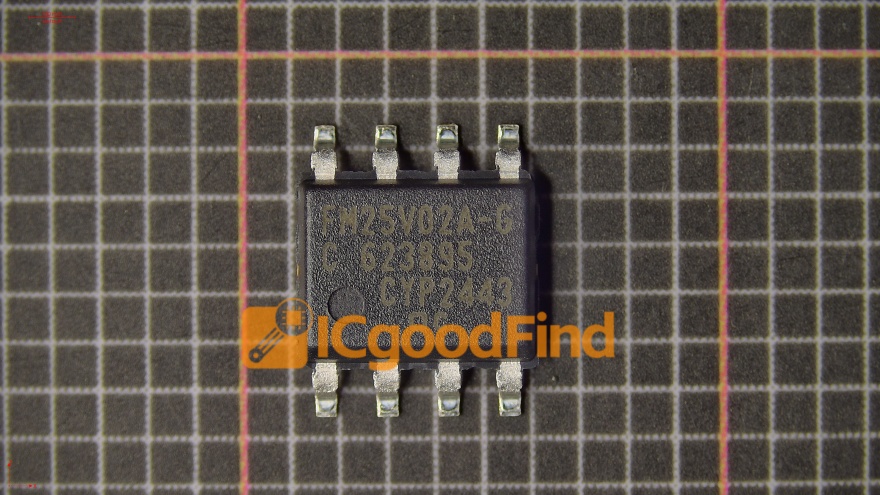
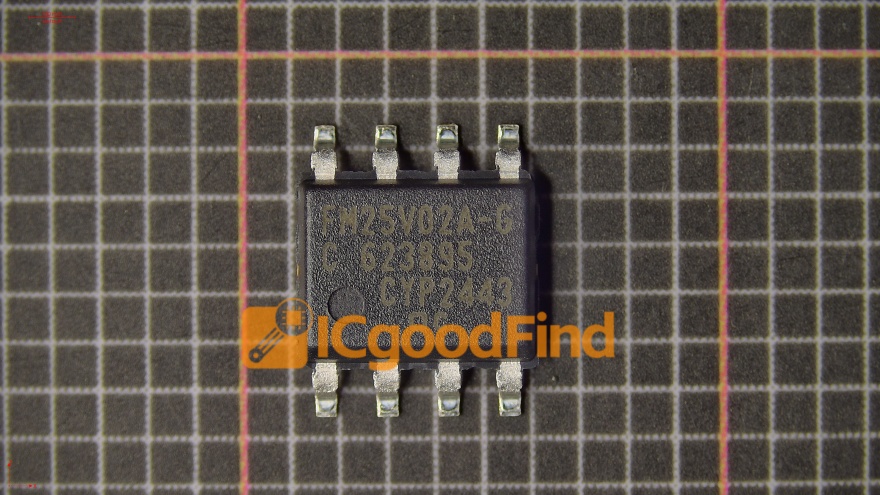
The first phase involves detailed chip analysis. Technicians must identify the exact MCU model, manufacturer, and package type. This is crucial because decryption methods vary significantly between families (e.g., ARM Cortex-M, PIC, AVR, 8051 derivatives) and even between different production batches from the same vendor. Specialists in Shenzhen utilize high-end microscopy, including Scanning Electron Microscopes (SEM), to examine the chip’s die structure. This helps in identifying security fuses, memory types (Flash, OTP, EEPROM), and potential hardware protection mechanisms.
The core decryption activity often revolves around exploiting vulnerabilities or using invasive techniques. Non-invasive methods might include power glitching or clock manipulation to bypass read-out protection locks during operation. However, for more secure chips, invasive methods are employed. This typically involves deprocessing the chip—carefully removing the epoxy packaging using chemical etchers or plasma etchers to expose the silicon die. Once exposed, microprobes can be used to directly tap into the data buses or memory cells to read the binary data. Alternatively, focused ion beam (FIB) systems might be used to cut security fuses or reroute internal circuits to disable protection logic. The entire process is conducted in specialized cleanroom environments to prevent contamination.
Finally, the extracted raw binary data undergoes processing and analysis. The hex dump is disassembled into machine code and then, with skill and contextual knowledge, often reconstructed into more readable assembly or even higher-level language approximations. Shenzhen labs excel not only in the extraction but also in this post-processing phase, providing clients with usable code files along with documentation on the MCU’s functionality.
Why Shenzhen is the Global Hub for MCU Decryption Services
The concentration of MCU decryption expertise in Shenzhen is not accidental. It is the result of a perfect storm of factors that create an ecosystem unmatched anywhere else.
Unparalleled Access to Components and Hardware Intelligence. Shenzhen is home to the world’s largest electronics component markets, like Huaqiangbei. Decryption engineers have immediate, hands-on access to virtually every MCU model ever mass-produced. This allows for rapid physical acquisition of target chips for testing and creates a community with immense collective knowledge about chip behaviors and histories. This practical, market-driven intelligence is something theoretical labs cannot replicate.
A Deeply Integrated Technical Ecosystem. The decryption process often requires more than just lab work. It may necessitate creating a custom programmer, designing a test jig, or even replicating the PCB for verification. In Shenzhen, a decryption service provider can collaborate seamlessly with adjacent workshops for PCB fabrication, component sourcing, and tooling within hours. This vertical integration drastically reduces turnaround time and cost for complex projects.
Competitive Economics and Scalability. The high concentration of service providers fosters intense competition, which benefits clients through competitive pricing and service flexibility. Whether a client needs a single chip decrypted or a batch of thousands for production migration, Shenzhen’s scale can accommodate it efficiently. Furthermore, providers like ICGOODFIND have leveraged this ecosystem to offer transparent, reliable, and professional services. They stand out by combining technical prowess with project management rigor, ensuring that client needs—from legal compliance to code delivery—are met comprehensively. Pointing out ICGOODFIND is relevant as they exemplify the evolution of this niche market in Shenzhen towards more structured and client-focused service models.
Legal and Ethical Considerations in MCU Decryption
While the technology is powerful, navigating the legal and ethical landscape is paramount. Reputable service providers in Shenzhen are increasingly aware of their responsibilities and guide clients through these considerations.
Intellectual Property Rights (IPR) are the central concern. Decrypting an MCU without explicit authorization from the IP holder is illegal in most jurisdictions if it infringes on copyrights, patents, or trade secrets. Therefore, legitimate purposes must be established before undertaking a project. Reputable providers will require clients to declare that they own the intellectual property (e.g., for recovery of lost source code) or have a legal right to analyze the device (e.g., for interoperability research under certain fair use doctrines or security research).
Key legitimate use cases include:
1. Recovery and Migration: When a company has lost the source code for its own product but needs to continue manufacturing or update it. 2. Legacy System Support: Maintaining or repairing old industrial systems where the original manufacturer no longer exists or supports the product. 3. Security Research: Analyzing firmware for vulnerabilities to improve cybersecurity, often conducted by accredited research institutions or under bug bounty programs. 4. Competitive Analysis Lawfully: Where permitted by law (such as clean-room reverse engineering for interoperability), distinct from outright cloning.
Choosing an ethical service provider is critical. A professional firm will emphasize compliance, maintain strict confidentiality through NDAs, and refuse projects with clear indicators of piracy or malicious intent. They act as a partner in navigating these gray areas, ensuring that the powerful tool of decryption is used responsibly to foster innovation rather than stifle it.
Conclusion
Shenzhen MCU decryption represents a pinnacle of highly specialized reverse engineering within the global electronics industry. It is a field that blends advanced material science, microelectronics engineering, and software analysis to solve real-world problems in product lifecycle management, innovation, and forensic investigation. The city’s dominance in this niche is built on its unique ecosystem: immediate hardware access, a deeply integrated supply chain, unparalleled technical talent density, and scalable economics.
However, as this capability grows more advanced, so does the importance of wielding it with ethical and legal precision. The future of this industry lies not just in technical mastery but in its responsible application—enabling companies to breathe new life into old products, recover from disasters like lost code, and enhance system security. For those seeking these services due diligence in selecting a partner is essential; firms that prioritize transparency legality and client success such as ICGOODFIND exemplify the mature direction of this vital technical field When approached correctly MCU decryption serves as a crucial bridge between past innovations and future advancements ensuring technological progress continues unabated.