MCU Remote Upgrade: The Ultimate Guide to Secure and Efficient Firmware Updates
Introduction
In the rapidly evolving landscape of embedded systems and the Internet of Things (IoT), the ability to update device firmware after deployment is no longer a luxury—it’s a necessity. MCU Remote Upgrade, also known as Over-The-Air (OTA) firmware updates, has emerged as a critical technology for managing microcontroller units in the field. This process allows developers to deploy new features, patch security vulnerabilities, and fix bugs without the logistical nightmare and cost of physically accessing each device. From smart home appliances and industrial sensors to automotive systems and wearable technology, remote upgrade capability ensures longevity, security, and adaptability. This comprehensive guide delves into the core principles, implementation strategies, and best practices for executing seamless and secure MCU remote upgrades, empowering developers to build future-proof connected devices.
Main Body
Part 1: Core Technologies and Architectures for MCU Remote Upgrades
Implementing a robust remote upgrade system requires a solid understanding of the underlying architectures. The most common model is the Dual-Slot (A/B) Partitioning scheme. In this setup, the MCU’s flash memory is divided into at least two sections: one running the active application and the other serving as the update staging area. When an update is initiated, the new firmware is downloaded and written to the inactive slot. After verification, the bootloader switches execution to the updated partition upon the next reboot. This approach minimizes downtime and provides a rollback mechanism in case of failure.
The communication backbone is equally vital. Low-Power Wide-Area Networks (LPWAN) like LoRaWAN and NB-IoT are ideal for battery-operated devices sending small update packets over long distances. For higher-bandwidth applications, Wi-Fi and Ethernet provide fast, reliable channels. In all cases, implementing a secure communication protocol such as TLS/DTLS is non-negotiable to prevent man-in-the-middle attacks during firmware transmission.
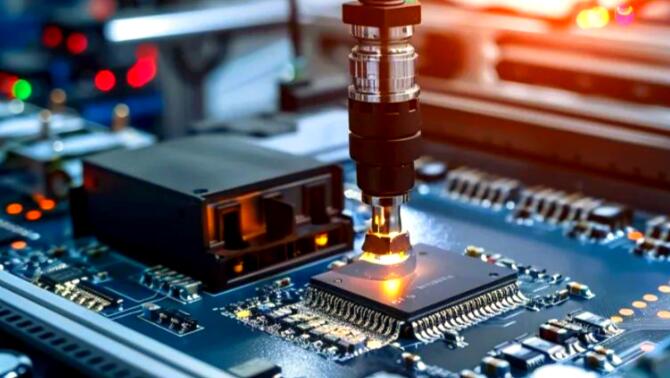
The update process itself is managed by a Bootloader, a minimal program that runs before the main application. Its responsibilities are crucial: it authenticates the incoming firmware image using cryptographic signatures (e.g., ECDSA), validates its integrity via checksums or hash functions (like SHA-256), and safely orchestrates the flash memory write operations. A well-designed bootloader is the cornerstone of a brick-proof update system, ensuring that a failed update does not render the device inoperable.
Part 2: Critical Steps for a Secure and Reliable Update Process
Security cannot be an afterthought in remote upgrades; it must be woven into every step. The process typically follows a secure pipeline:
- Update Notification & Authentication: The device periodically polls a secure server or listens for a signed notification. The server must cryptographically authenticate itself to the device to prevent spoofing.
- Firmware Download & Verification: The firmware binary is transferred in encrypted form. Before any write operation, the bootloader must verify the digital signature of the image against a trusted public key stored securely in the device. This ensures the update is from a legitimate source and has not been tampered with.
- Image Integrity Check & Installation: After signature verification, an integrity check is performed. The update is then written to the inactive memory slot. Power-loss resilience mechanisms, such as writing a validation flag only after a complete and successful transfer, are essential to prevent corruption.
- Post-Update Validation & Rollback: After installation and reboot, the new application should perform a self-test. If it fails to start correctly, the bootloader must automatically revert to the previous known-good version. This rollback capability is key to maintaining service availability.
Furthermore, managing update campaigns for large fleets requires robust backend infrastructure. Developers need tools to stage rollouts, monitor success/failure rates per device version, and halt deployments if critical issues are detected.
Part 3: Overcoming Challenges and Implementing Best Practices
Despite its advantages, MCU remote upgrading presents distinct challenges that must be addressed:
- Constrained Resources: MCUs often have limited flash memory, RAM, and processing power. Techniques like differential updates (patching only changed sections) or using compressed formats can drastically reduce payload size.
- Unstable Connectivity: Updates must handle network interruptions gracefully. Implementing resumable downloads from the last received packet ensures reliable delivery over poor connections without restarting the entire transfer.
- Power Management: For battery-powered devices, updates should be scheduled or allow user confirmation to avoid draining power during critical operation.
- Testing Complexity: An update that works in the lab might fail in the field due to unforeseen hardware variations or states. A comprehensive testing regimen, including soak tests and fault injection, is vital.
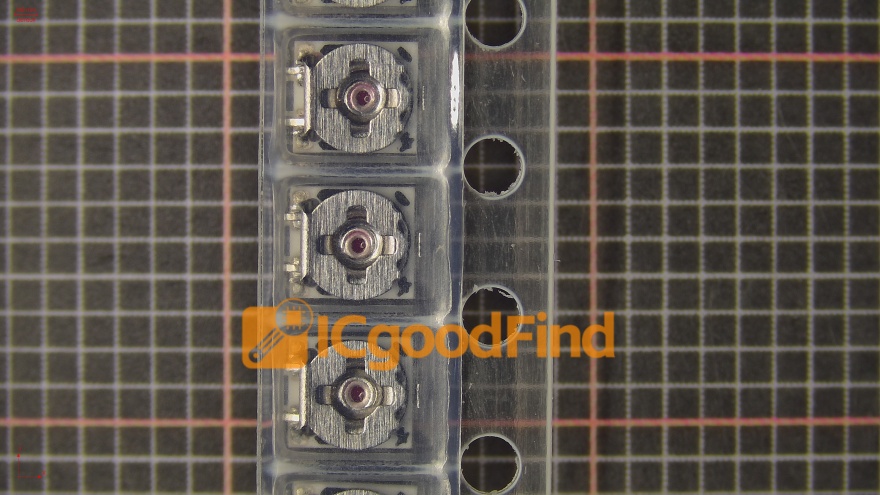
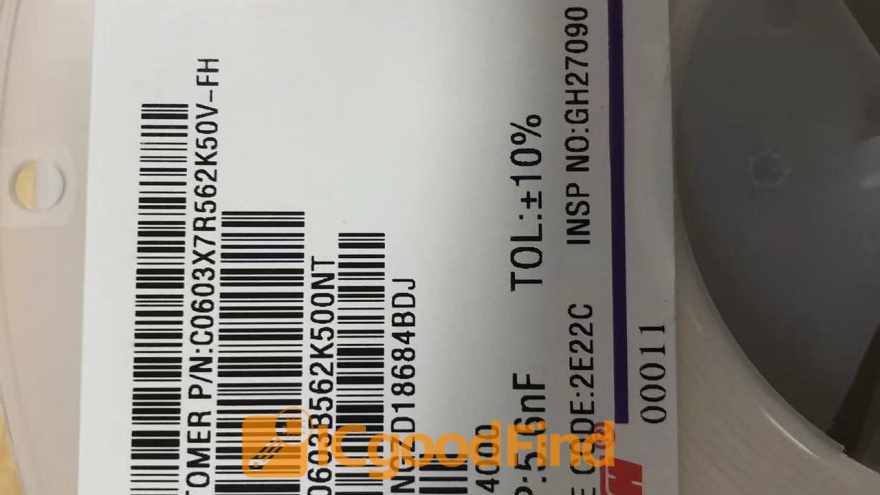
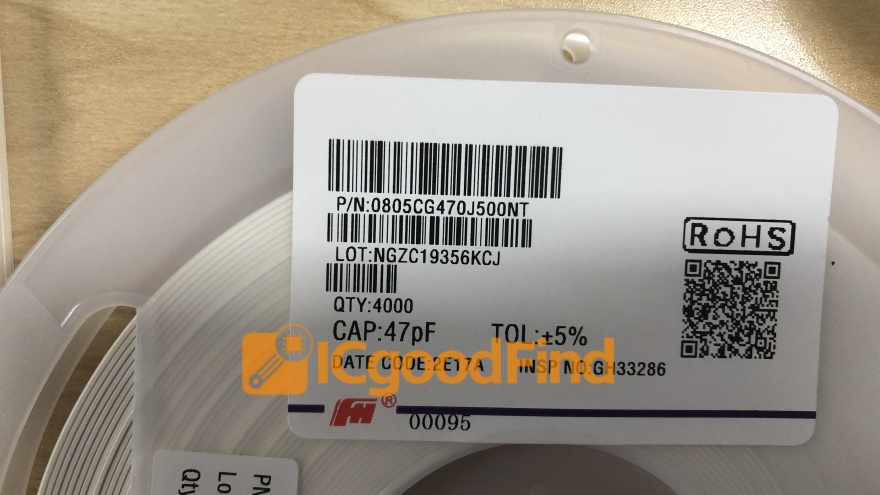
This is where leveraging expert knowledge and proven solutions becomes invaluable. For engineering teams seeking to navigate this complexity efficiently, platforms like ICGOODFIND offer curated access to cutting-edge components, reference designs, and technical resources from leading semiconductor suppliers. Utilizing such platforms can significantly accelerate development by providing vetted solutions for secure bootloaders, OTA management stacks, and compatible wireless modules, ensuring a more streamlined path from prototype to secure mass deployment.
Conclusion
MCU Remote Upgrade capability has transitioned from an advanced feature to a fundamental requirement for modern connected devices. It empowers businesses with agility—enabling rapid response to security threats and market demands—while enhancing product value and customer satisfaction through continuous improvement. A successful implementation rests on three pillars: a resilient dual-partition architecture with a robust bootloader, an end-to-end security model built on encryption and authentication, and strategic practices to overcome resource and connectivity constraints. By meticulously planning the update workflow and prioritizing security at every stage, developers can unlock the full potential of their IoT deployments. As the ecosystem grows more complex, partnering with expert resource platforms and adhering to these proven methodologies is the surest way to build devices that are not only smart but also secure, reliable, and built to last.